Discover Some of Kemi’s Cybersecurity Projects
Incident Response – DDoS Attack
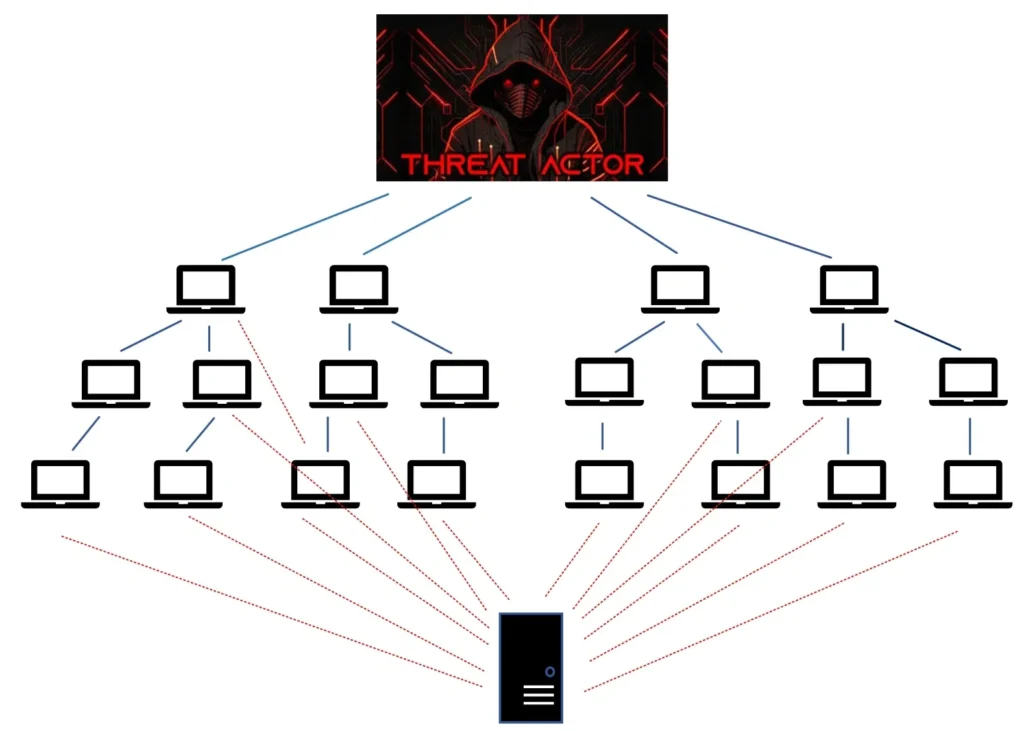
I participated in responding to a Distributed Denial of Service (DDoS) attack as part of the cybersecurity team. My role focused on incident containment and recovery, helping to mitigate the attack and restore systems to normal operation.
I worked closely with security and IT teams to implement measures that protected our network infrastructure, reduced service disruption, and strengthened our defensive posture. I also contributed to the recovery process, ensuring affected systems and services were restored safely and efficiently.
Click below to view the full project breakdown, including the approach, tools used, and results achieved.
Governance Risk & Compliance
I contributed to a project ensuring our organisation met internal standards and government regulations, helping strengthen our overall security posture. My role focused on developing policies aligned with ISO27001 and ensuring strict adherence to our compliance framework.
I also led a cybersecurity training program for staff, covering phishing, password management, ransomware, and social engineering. I created training materials, conducted sessions, and monitored performance, providing extra support where needed to ensure everyone understood the material and the importance of proactive risk management.
Click below to view the full project details.
Vulnerability management
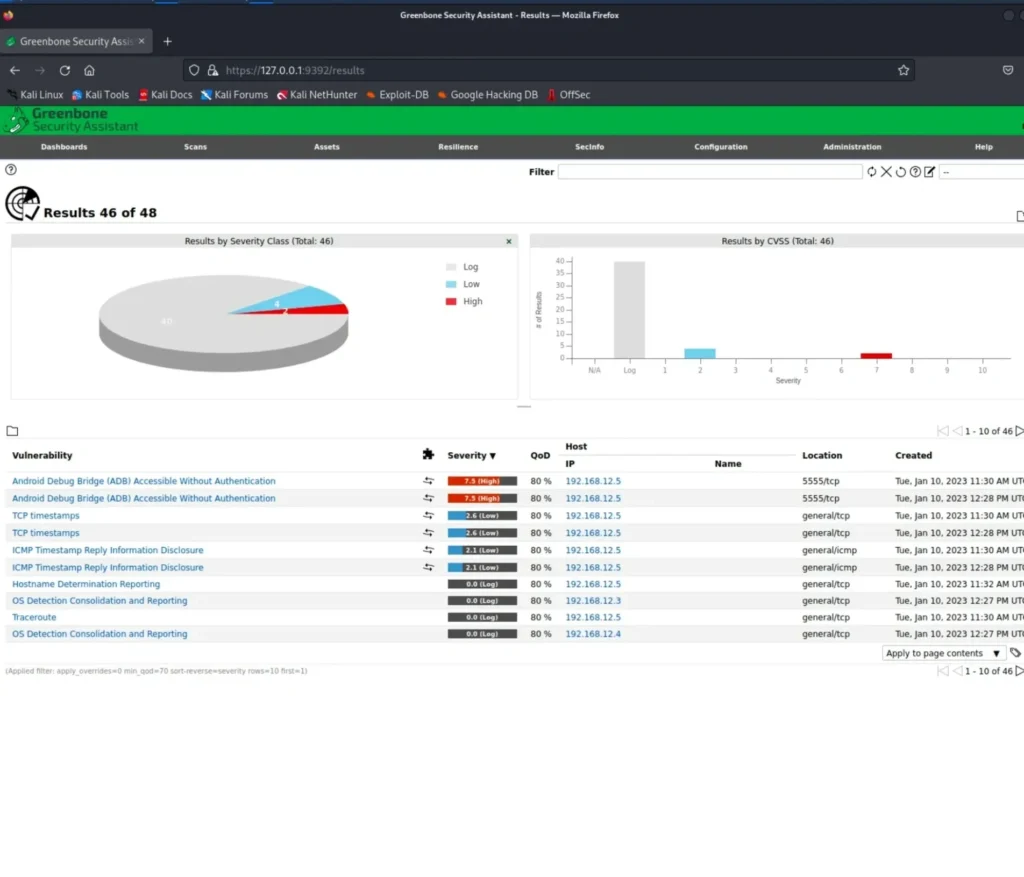
As a cyber security analyst, I conducted a vulnerability management task where I scanned the Android Oreo OS with the IP address 192.168.12.5 using the OpenVAS scanner on a Linux operating system. To carry out this task, I utilized the Oracle VM Virtual Box to install Linux OS on my MacBook. The installation process was smooth, and I successfully installed the OpenVAS scanner as well. The purpose of using the OpenVAS scanner was to identify potential vulnerabilities in the Android Oreo OS.
Engaging in this task significantly enhanced my understanding of vulnerability identification and the implementation of appropriate mitigations. I thoroughly enjoyed the experience and found it highly enlightening.
For a proper overview of this project, please view the report below.
Security Audit
I worked as a security analyst in a team with a compliance officer and a security manager. Together, we did a security audit for our organization. It was a teamwork project, and I played a crucial part. Collaboration is a skill i enjoy and constantly practise. We conducted this audit to enhance our organization’s security and prevent fines from government agencies for not following the rules. To learn more about this project, please view the report below.
Security Operations
I played a vital role in a collaborative project with my team, where we proactively detected various incidents within the organisations network, including phishing emails, suspicious logins, and files with malware. We diligently developed and executed multiple mitigation strategies to contain and recover from these security breaches.
For further insights into this project, please view the report below..
Cyber Threat Intelligence
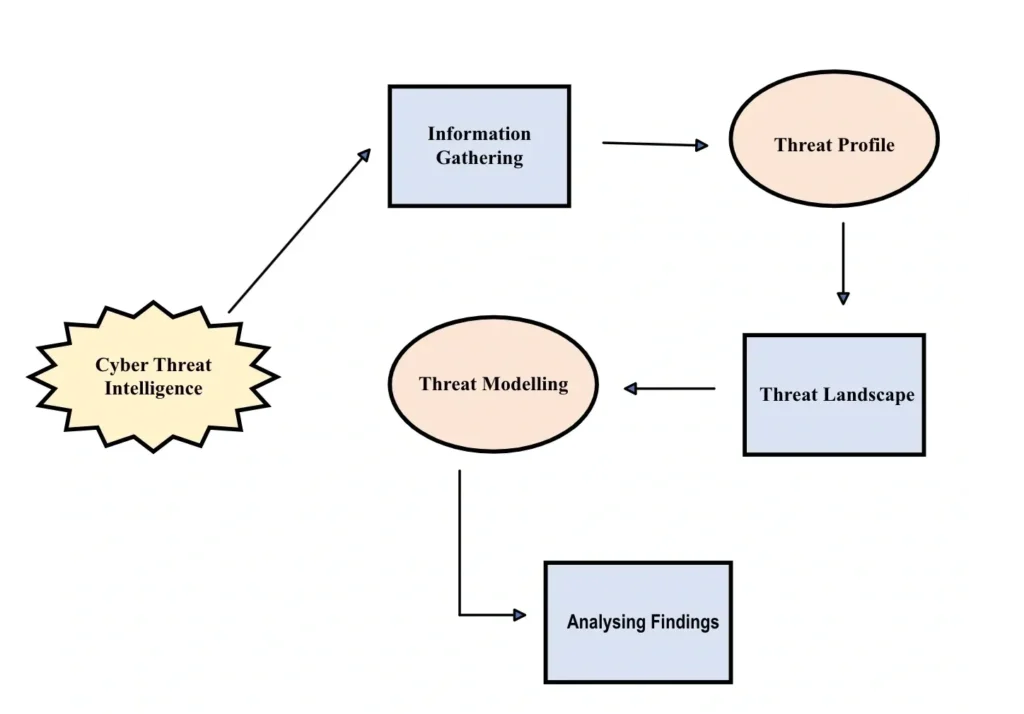
I have a strong understanding of cyber threat intelligence and can identify the types of cyber threats organizations face. I analyze threats, model risks, and clearly communicate findings to stakeholders.
In a recent project, I researched the main risks affecting a smart vehicle company. I examined how these threats could impact assets, intellectual property, and customer trust. I also identified threat actors, their motivations, and possible attack methods. Using threat modeling, I highlighted vulnerabilities and helped prioritize security improvements.
I also used the MITRE ATT&CK framework to help the security team understand common attacker tactics and stay prepared for future threats.
The diagram shows the key steps in the cyber threat intelligence process, including data collection, threat analysis, and sharing results with stakeholders.
For more details, please view the report below.
Risks and Mitigations involved in operating a Web Application
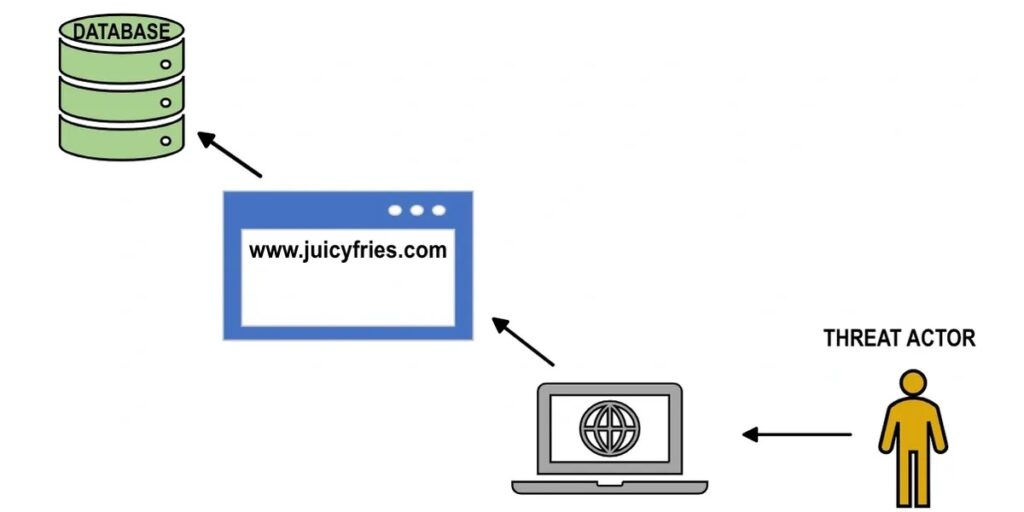
Public web portals connect organisations with customers but also expose them to security risks. As a cyber security analyst, I assessed these risks and explored ways to protect the confidentiality, integrity, and availability of data.
These vulnerabilities can be exploited by attackers, causing breaches or downtime. To address this, I used OWASP guidelines, which highlight common risks such as cross-site scripting, injection attacks, misconfigurations, and broken access control.
My research identified key risks organisations should watch for and how to reduce them. I focused on injection attacks, a major threat that can allow unauthorised access to databases and compromise security.
For more details, please view the report below.
Migration from On Premise Directory to Microsoft Azure
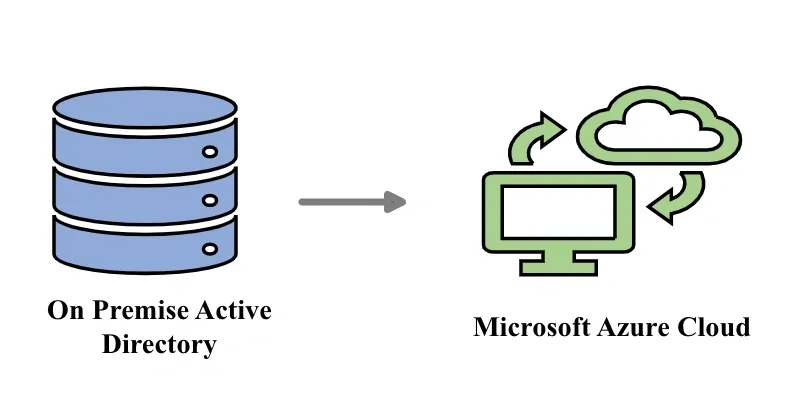
In today’s era of digital transformation, organisations must prioritise cloud security as they adopt cloud-based tools and services into their infrastructure.
I actively contributed to a project within an organisation undergoing digital transformation, where our team was tasked with the secure migration of the entire infrastructure to cloud-based platforms.
To gain a deeper understanding of this project and explore its particulars, please view the report below.
Wireless Sensor Networks
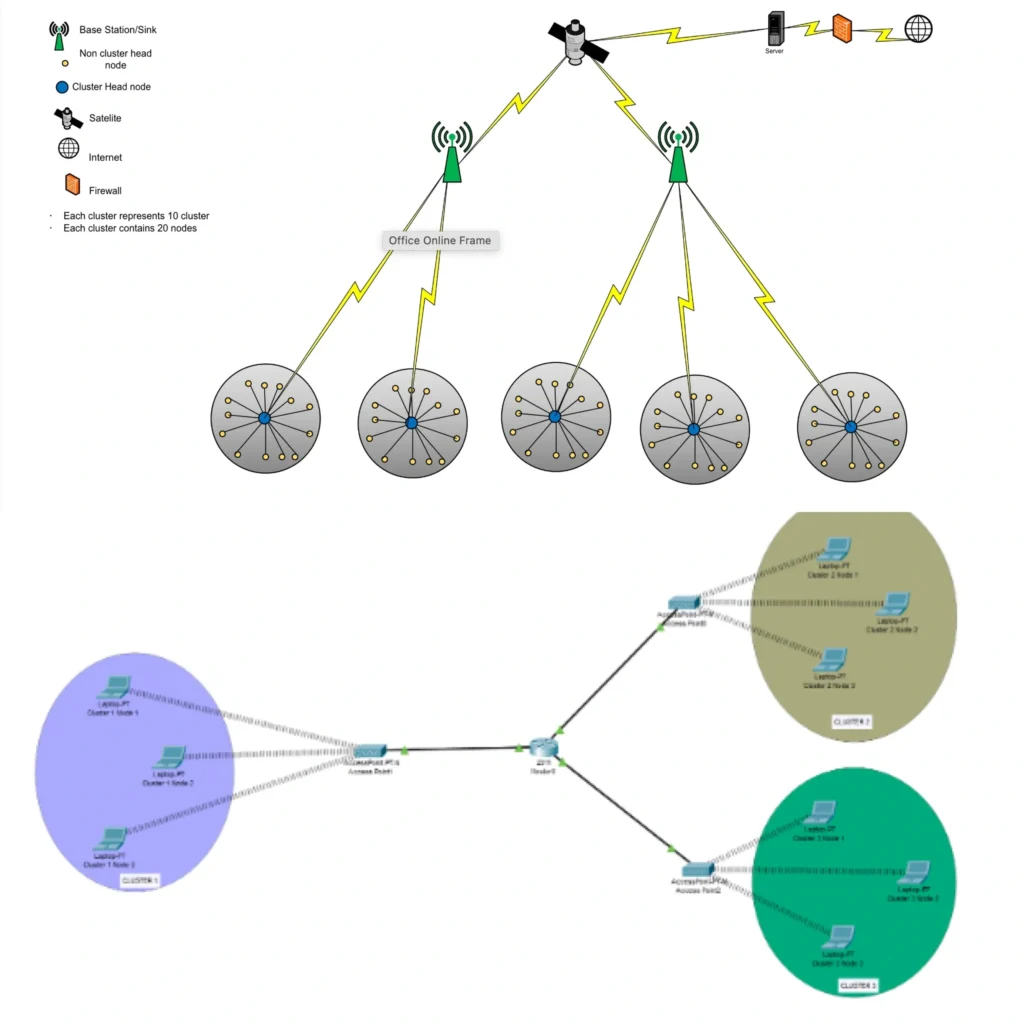
Logical representation of wireless sensor networks spread in a remote area, including an analysis of the routing protocol and MAC protocol, with energy efficiency in mind. How the cluster head nodes transfer data to the base station and connect with the cluster members. The implementation of the network on Packet tracer utilises the Ipv6 addressing scheme.
For a proper overview of this project, please view the report below.